Let’s walk through a standard two-factor authentication registration.
The user creates an account and provides a phone number. A one-time passcode is sent to that phone number, and after the OTP is entered, the account is verified. The user now has full access to the platform.
Now let’s walk through what didn’t happen.
In the previous example, we didn’t learn anything about the phone number. We don’t know who it belongs to or to which device it is connected. We don’t even know what type of phone number it is. We only know that it was a phone number the registrant had access to at least for a moment.
Why is this important?
At first glance, one might think this wouldn’t be a concern for a platform. After all, registration conversions lead to growth and growth leads to profits, right? Not necessarily. Let’s provide another example.
In this scenario, a user registers a new account on an eCommerce site. They provide a phone number, enter an OTP, and gain access to the ecosystem. Only this particular account was registered using a VoIP number. This user registered several accounts with several VoIP numbers that they procured for free from the internet. This fraudster’s next move is to post dozens of fake reviews on his product, rocketing his item to the eCommerce platform’s first page by cheating the algorithm.
VoIP numbers, burner phones, SIM cards belonging to a SIM farm; all these phone number types are heavily associated with fraud. Fraudsters know that phone numbers are typically a unique identifier. That no longer becomes the case when they can acquire numerous free numbers with dubious intent.
These accounts created with fraudulent intent we refer to as fake accounts and they can cause problems in almost any industry. With social media, fake accounts are used to spread misinformation. With marketplace, gaming, or on-demand services, fake accounts are heavily associated with credit card fraud. In the financial services sector, a fraudster might use a blend of real and fake information to practice synthetic identity fraud which often preys on children’s pristine credit scores. Rest assured, fake accounts are bad. Fortunately, there is a digital identity step we can add to the registration process that occurs seamlessly in the background without providing additional friction.
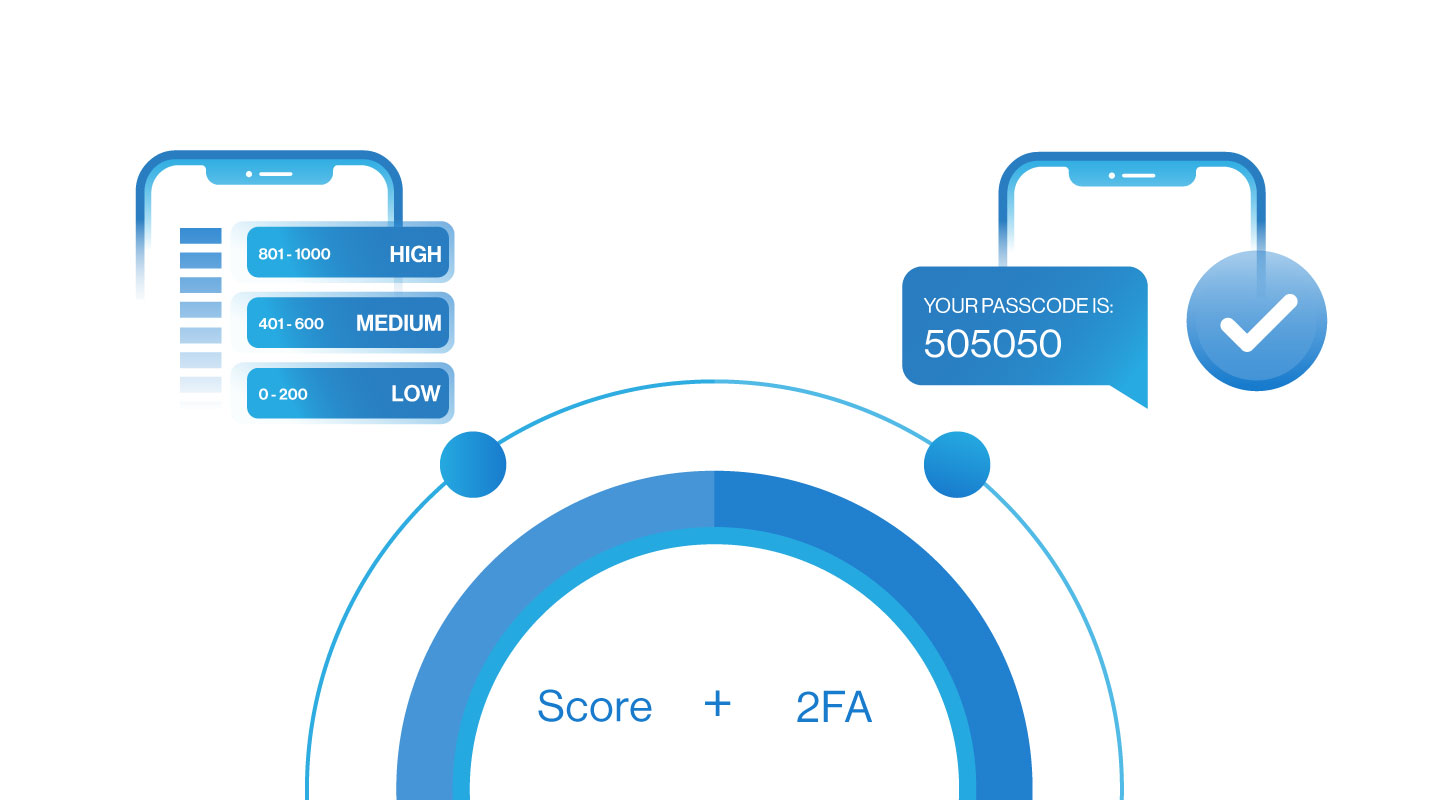
2FA + Score
Score is an identity solution that delivers reputation scoring based on digital intelligence, traffic patterns, machine learning, and a global data consortium. When looking at the available information on a user, dozens of data points exist to deliver a digital footprint. Score takes a holistic look at a user’s digital identity and assesses a score based on its likelihood of committing fraud. Certain aspects that Telesign deems risky, result in a higher score. What types of behavior would negatively impact a user’s score? A VoIP phone number, a burner phone, a phone number that has recently changed devices (SIM Swap).
This check is done instantaneously in the background at registration and the platform can act on the results. Often, platforms will block a registration if the fraud score is too high, or at the very least flag the registration for a manual review. Good users are validated with no additional friction, and platforms can rest easy to keep hazardous fake accounts off their platform.
If we go back to our original example of the fraudster trying to register an account with a VoIP phone number, we see that Score would block this registrant, restoring trust to the platform. When paired with 2FA, Score is the ultimate gatekeeper for digital platforms.
Telesign has been connecting and protecting online experiences for over 15 years. We support the largest web properties in the world and we’re prepared to help you. Contact Telesign now and for all of your security needs. As the pioneers of phone-based security, we are a one-stop-shop for all of your digital identity and programmable communications needs.